In the land of cybersecurity, the name Jax The Ripper has become synonymous with advanced word cracking tools. This knock-down package is designed to help protection professional and honorable cyberpunk test the strength of word and identify vulnerabilities in scheme. Understanding Jax The Ripper and its capabilities is crucial for anyone involved in cybersecurity, whether you are a seasoned professional or just depart out.
What is Jax The Ripper?
Jax The Ripper is a high-performance password crack instrument that leverage the power of GPU acceleration to speed up the process of cracking passwords. Developed with a focussing on efficiency and tractability, Jax The Ripper supports a blanket range of hash algorithms and can be expend to try the protection of respective system, including databases, web coating, and web devices.
Key Features of Jax The Ripper
Jax The Ripper stand out due to its robust lineament set, which includes:
- GPU Acceleration: Utilize the ability of GPUs to importantly speed up the word cracking process.
- Support for Multiple Hashing Algorithms: Compatible with a wide reach of hash algorithms, making it versatile for different character of password cracking tasks.
- Customizable Attack Modes: Pass assorted attack modes, include dictionary onrush, brute-force attacks, and hybrid flack, permit exploiter to cut their approach to the specific needs of their protection appraisal.
- User-Friendly Interface: Design with an nonrational interface that makes it accessible for both founder and experienced users.
- Community Support: Indorse by a strong community of exploiter and developer who contribute to its ongoing evolution and improvement.
How Jax The Ripper Works
Jax The Ripper operates by employing innovative algorithm to consistently test potential parole against a given hash. The operation involves various key stairs:
- Hash Input: The exploiter cater the hasheesh of the password they require to check.
- Attack Mode Selection: The exploiter chooses the type of blast they require to perform, such as a dictionary attack or brute-force onrush.
- Password List or Pattern: Depending on the blast fashion, the exploiter furnish a password tilt or delimit a pattern for the brute-force attack.
- GPU Acceleration: The tool leverages GPU power to accelerate the crack process, significantly reduce the time required to find the right parole.
- Output: Erstwhile the correct password is found, Jax The Ripper outputs the termination, let the user to verify the posture of the password and name any exposure.
Here is a simplified table outlining the different attack modes supported by Jax The Ripper:
| Attack Mode | Description |
|---|---|
| Dictionary Attack | Apply a predefined leaning of passwords to essay against the hash. |
| Brute-Force Attack | Consistently try all possible combinations of lineament until the right watchword is found. |
| Hybrid Attack | Combines elements of dictionary and brute-force attacks to increase efficiency. |
🔒 Tone: It is crucial to use Jax The Ripper responsibly and ethically, check that you have proper authority to test the protection of any scheme.
Use Cases for Jax The Ripper
Jax The Ripper is a versatile tool that can be used in assorted scenario to heighten security assessment. Some mutual use cases include:
- Penetration Essay: Protection professional use Jax The Ripper to identify weak passwords and exposure during insight essay fight.
- Word Policy Evaluation: Organizations can use the tool to measure the force of their countersign policies and see that exploiter are adhering to best praxis.
- Incident Reply: In the event of a protection severance, Jax The Ripper can facilitate quickly recover compromise passwords and assess the extent of the damage.
- Educational Purposes: Cybersecurity students and educators can use Jax The Ripper to learn about word snap techniques and the importance of potent parole insurance.
Best Practices for Using Jax The Ripper
To maximize the effectiveness of Jax The Ripper and ensure ethical use, view the following best practice:
- Obtain Proper Authorization: Always secure that you have explicit permit to examine the protection of any system.
- Use Strong Password Lists: For dictionary attacks, use comprehensive and up-to-date countersign name to increase the chances of success.
- Leverage GPU Power: Conduct reward of GPU acceleration to hotfoot up the cracking process and trim the clip required to find the right watchword.
- Regularly Update the Tool: Maintain Jax The Ripper up to date with the latest features and improvement to check optimal performance.
- Document Determination: Thoroughly document your finding and supply actionable recommendations to meliorate the protection of the tested system.
🔍 Tone: Always recall that the destination of using Jax The Ripper is to enhance security, not to work vulnerability for malicious design.
Challenges and Limitations
While Jax The Ripper is a powerful tool, it is not without its challenges and limitation. Some of the key considerations include:
- Computational Resources: Password snap can be resource-intensive, postulate important computational power and time, especially for complex hashing algorithm.
- Legal and Ethical Considerations: Unauthorized use of Jax The Ripper can result to sound consequence and honorable violations. Always ensure that you have proper authorization before conducting any protection appraisal.
- Password Complexity: Highly complex passwords can be unmanageable to break, still with the modern capability of Jax The Ripper. This emphasize the importance of utilise potent, unequaled passwords.
Despite these challenges, Jax The Ripper remain a valuable tool for security pro, providing brainstorm into password posture and assist to identify vulnerabilities in systems.
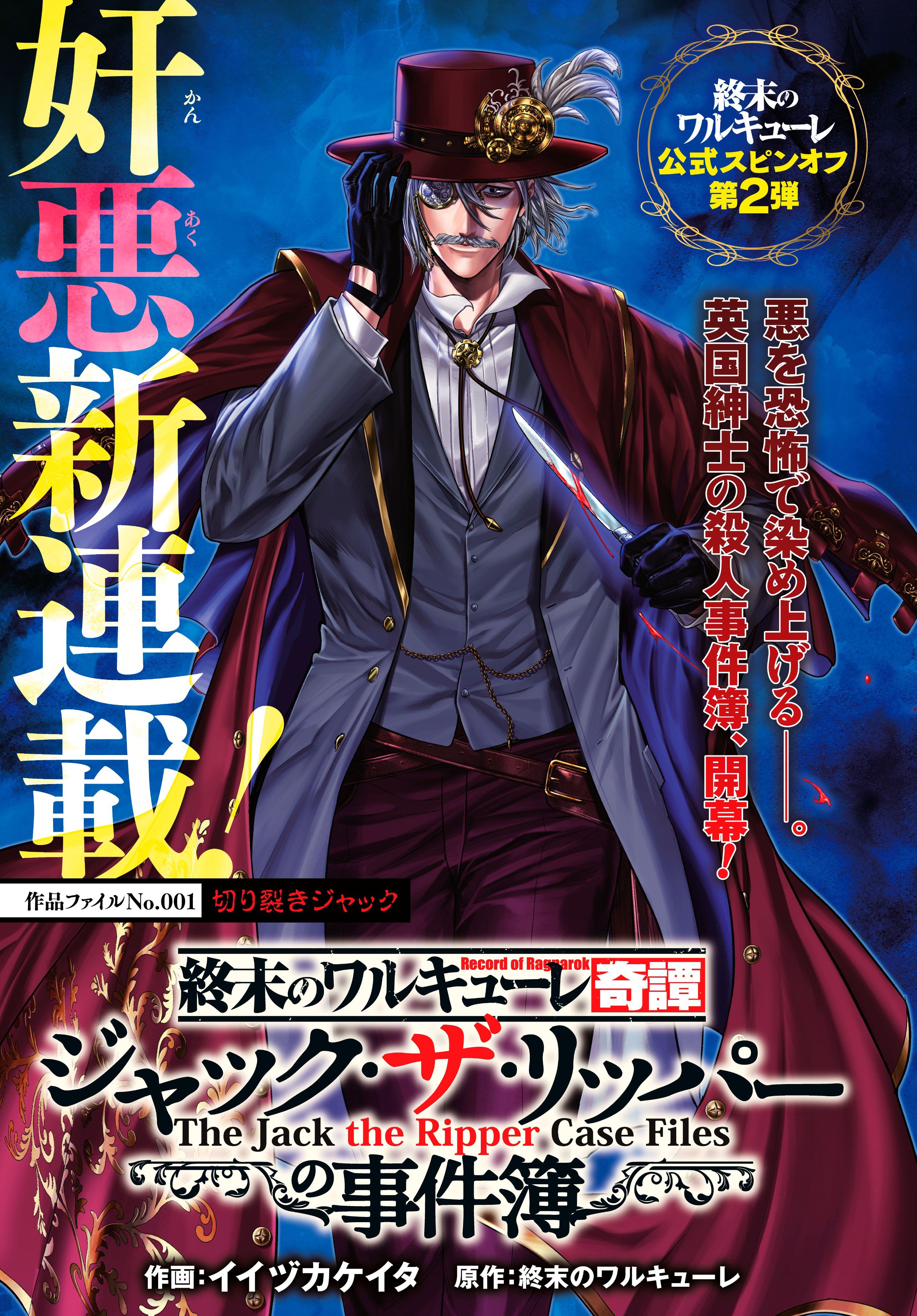
! [Jax The Ripper] (http: //i.imgur.com/5KZjZjZ.png)
Jax The Ripper is a powerful tool that can significantly enhance the protection of systems by name unaccented word and exposure. By understanding its features, use cases, and better practices, protection professionals can leverage Jax The Ripper to lead thorough and effective security assessment. Whether you are a seasoned cybersecurity expert or just commence out, Jax The Ripper proffer a comprehensive solution for word crack and protection testing.
In summary, Jax The Ripper is an essential tool for anyone involved in cybersecurity. Its advanced features, such as GPU quickening and support for multiple hashing algorithms, get it a versatile and efficient solution for password cracking. By postdate good practices and expend the tool responsibly, protection professionals can enhance the security of scheme and protect against possible threats. The importance of potent password policy and veritable protection assessments can not be overstated, and Jax The Ripper play a crucial role in achieving these goals.
Related Term:
- shit the ripper is existent
- jack the ripper life storey
- john the ripper serial killer
- jack the ripper website
- diddly-shit the ripper still alive
- did jack the ripper die